
BioTone
Five biometrics. One smartphone. Zero specialized hardware.
Credentials are the #1 attack vector
Turn any smartphone into a biometric identity device
6 Independent Signals, 2 Auth Factors
Iris, palm, ear, voice, PPG pulse, and selfie liveness — six signals spanning something you are and point in time. Device attestation and geofencing extend to 4 factors.
Standard Smartphone
No IR scanners, no vein sensors, no fingerprint readers. Uses the cameras and microphone already in every modern phone.
Multiplicative Security
Compromise one signal, learn nothing about the others. An attacker must defeat 3+ unrelated modalities simultaneously.
Layers On Top
Auth broker pattern — no rip-and-replace. Compatible with existing SSO, ICAM, CAC/PIV, and zero trust frameworks.
Six signals, independent sensors, zero correlation
Iris
Front camera
30% weight
0.75% EER
Voice
Microphone
25% weight
0.30% EER
Palm
Rear camera
25% weight
4.27% EER
Ear
Front camera
20% weight
8.09% EER
PPG Pulse
Rear camera
Liveness gate
All processing on-device. Raw biometric data never leaves the phone.
Iris
Phase-structure encoding from visible-light capture.
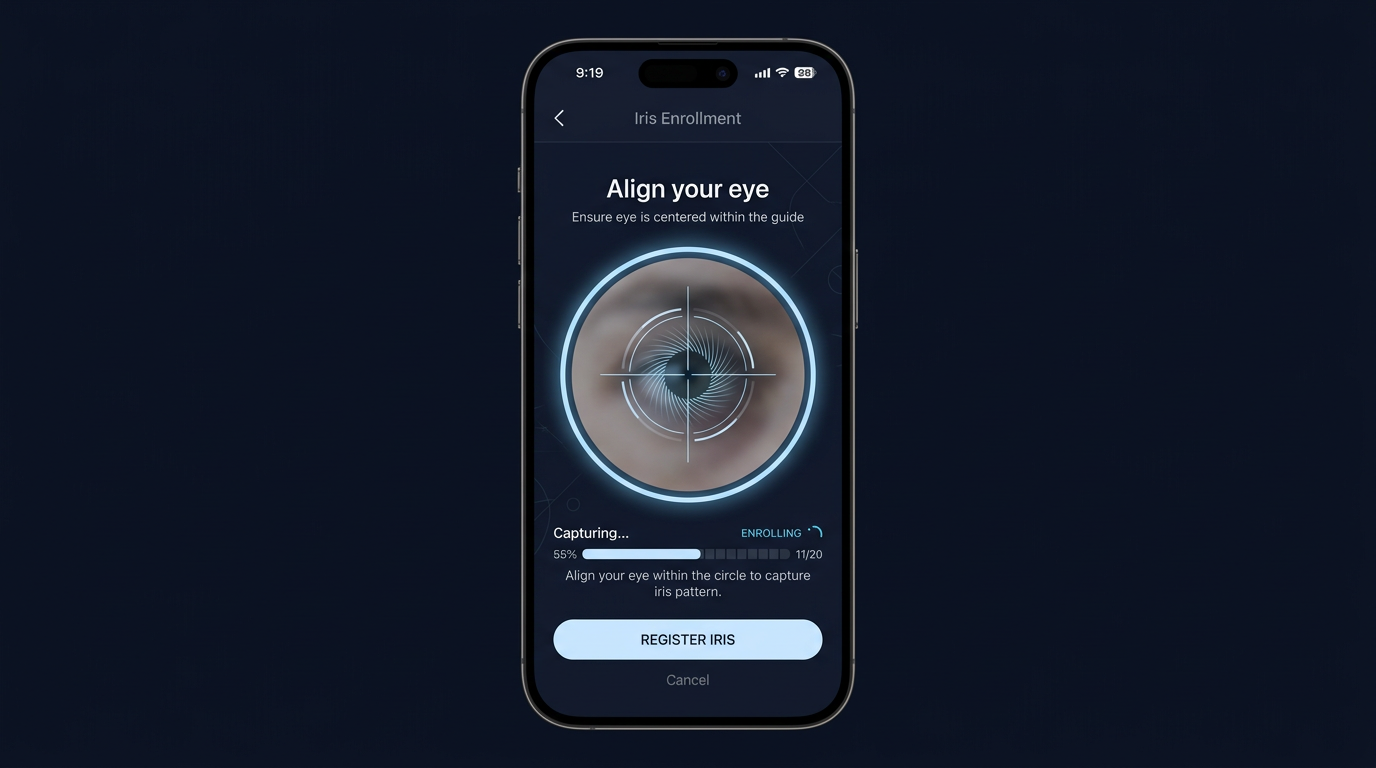
Placeholder UI — drop in a real app screenshot at signals/iris.png before presenting.
Palm
Texture and line structure from contactless palm imaging.

Placeholder UI — replace with signals/palm.png when ready.
Voice
Speaker embedding with time-bound digit challenge.

Placeholder UI — replace with signals/voice.png when ready.
Ear
Cartilage geometry from profile capture.
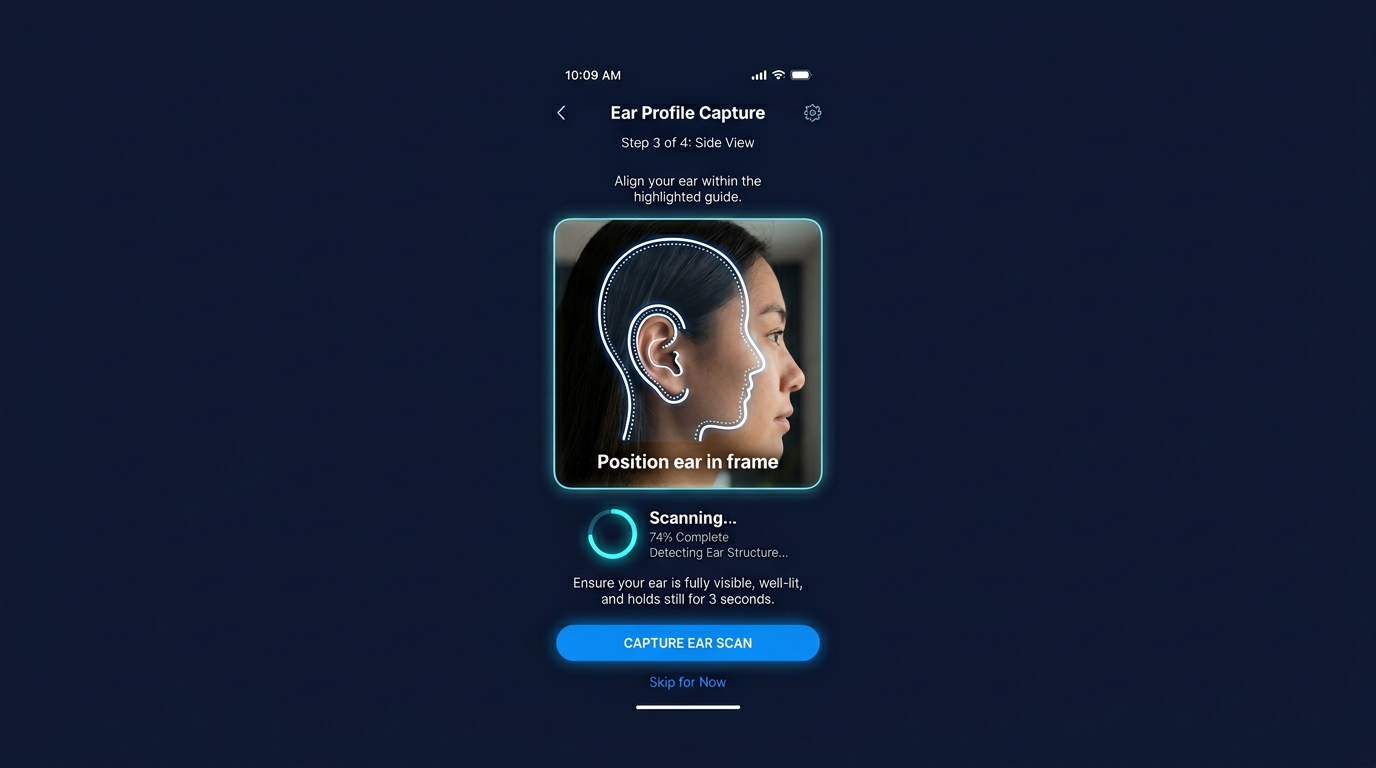
Placeholder UI — replace with signals/ear.png when ready.
Vitals (PPG)
Pulse-based liveness via camera; vetoes non-living presentation.

Placeholder UI — replace with signals/vitals.png when ready.
Presentation
Active liveness challenges (e.g., blink, motion) per session.

Placeholder UI — replace with signals/presentation.png when ready.
Three independent liveness gates
Selfie Liveness
Random blink + head turn challenges. Must respond in real time within a timeout window.
Defeats: photos, masks, screen replays
PPG Pulse Gate
Detects cardiac blood pulse through fingertip. Vetoes entire authentication if no live pulse.
Defeats: all non-living artifacts
Voice Challenge
Time-bounded rotating 6-digit code (30s window). User must speak the current code live.
Defeats: pre-recorded audio replay
All liveness gates must pass. A perfect biometric match is rejected if liveness fails.
Multiplicative security from independent factors
Fusion requires weighted majority of factors to pass AND all liveness gates to pass. Learned score-level fusion further improves combined accuracy.
Per-factor FAR thresholds are each factor's measured equal-error-rate operating point (see next slide); combined FAR assumes factor independence. Strict AND FAR = product of per-factor EERs. Combined d′ ≈ 10.05, indicating strong discriminability. Not NIST Biometric Evaluation Program results; independent validation scoped for pilot phase.
Held-out EER per factor — production-faithful
Same benchmarks, same held-out subjects, same enrolment protocols the app actually ships.
All four identity factors now have measured held-out EERs. Iris ships a custom visible-light deep embedding model. Voice runs at published WeSpeaker SOTA. Palm and ear each deliver >2× EER reductions vs. previously-shipped models.
Protocol C / D′: k-frame or k-utterance enrolment averaged-and-renormalized, probed against gallery (matches the app's enrol flow). Protocol A single-frame references: iris 1.44%, voice 0.87%, palm 9.75%, ear 13.18%. All measurements held-out on subjects never seen during training; raw results in benchmarks/{voice,palm,ear,iris}/.
Why multi-factor beats single-factor hardware
✗ One point of failure — defeat it, full access
✗ Requires $1,000+ specialized devices
✗ No server-side identity or enterprise control
✗ Platform-locked (iOS only for Face ID)
✓ Must defeat 3+ modalities simultaneously
✓ Any modern smartphone — $0 new hardware
✓ Server-side identity, full enterprise control
✓ iOS + Android, cross-platform
Security through factor independence, not hardware specialization.
Zero-storage, three-part key disaggregation SHIPPED
Shamir 3-of-3 secret sharing — all three parts required. BioTone never stores biometric templates or key material.
Customer Primary Server
On-premises or self-hosted node. Holds Key Share 1. Verified via auth broker flow.
Customer Cloud
Azure, AWS, Oracle, or Google — customer's choice. Holds Key Share 2.
User's Device
Enrolled phone's secure enclave (Keychain/Keystore). Holds Key Share 3. Bound at enrollment.
No single party — including BioTone — can reconstruct a template or authenticate on behalf of a user. Key verification integrated into the auth broker token.
- FIPS 201
- NIST SP 800-76
- DoD 8520
- NIST SP 800-207 Zero Trust
Architecture designed for alignment with federal identity and biometric standards. Formal validation scoped during pilot engagement.
Encryption standards — no ambiguity
At Rest
AES-256-GCM for all biometric template data and disaggregated key parts. Each key part independently encrypted at its storage location.
In Transit
TLS 1.3 for all API communication. Certificate pinning on mobile clients. No biometric data transmitted — only assertion tokens.
On Device
Hardware-backed storage: iOS Secure Enclave (Keychain) and Android TEE (Keystore). Key Part 3 never leaves hardware security boundary.
- AES-256-GCM
- TLS 1.3
- FIPS 140-2 validated modules
- FIPS 140-3 (roadmap)
- CNSA 2.0 ready
Uses FIPS 140-2 validated cryptographic libraries (Apple CryptoKit, Android Keystore). Full FIPS 140-3 module validation scoped for pilot phase. Architecture supports CNSA Suite 2.0 cipher selection for NSS environments.
Auth broker — layers on top of existing systems
Identity Providers
Entra ID (live today)
Okta + Ping (near-term)
Standard OIDC / SAML
Token Standards
JWT (HS256) with jti, aud, TTL/validate · /introspect · /.well-known
CAC / PIV
Complementary factor alongside physical credentials
Tactical Edge
Offline-capable with cached credentials
Customer deploys our server software on their infrastructure. Demo app live at demo.biotonebiometrics.com. Data and liability stay with the customer.
Continuous re-authentication — not just point of entry
Session confidence decays over time. Multi-signal architecture enables tiered re-verification from passive to active.
Policy-configurable per security context. SCIF, enterprise, and tactical edge each get the cadence their threat model requires.
Flexible deployment for any environment
Enterprise On-Premises
Customer-hosted backend on government or corporate infrastructure. Full data sovereignty.
Government Cloud
Azure Gov, AWS GovCloud, or customer-specified environment at IL5. FedRAMP High / GCC High on roadmap.
Tactical Edge
On-device verification with locally cached credentials. Trades disaggregation for offline capability. Policy-controlled session limits. Syncs when connected.
BYOD / Shared Facility
Device enrollment binds identity to a specific phone. Re-enrollment required for device change.
Production-ready — deployed and running
/validate, /introspect, /.well-knownconsole.biotonebiometrics.com — users, sessions, config, deployment, auditwww.biotonebiometrics.com + demo.biotonebiometrics.comTimeline from PoC to pilot is driven by customer requirements. We move at your pace.

BioTone
Five biometrics. One smartphone. Zero specialized hardware.
Roger Ach
CEO, BioTone Corporation
Benjamin Portman
CTO, Engineering Lead
Confidential — shared for evaluation purposes